With such alarming rates of data creation, minds need to be put to use to think about reliable data destruction as well. No one would ever want their personal, utmost confidential data to be leaked or misused in unimaginable ways. Corporate, especially MNCs and large-scale companies, need to ensure that their data is properly secured and destructed in order survive today’s competitive environment and maintain information secrecy.
In today’s scenario, following the tried and tested good practice guidelines for secured digital data management is a must. It is the new law! But at the same time, it is a well-accepted fact that the higher the sensitivity of data involved, the higher is the risk of security issues. These risks can arise due to data disclosure owing to the inappropriate deletion of data, or poor destruction of media before its disposal. Such leakage of data can even occur through computers sent for recycling purpose. Hence, secured digital data destruction is the new norm!
Data destruction is much more than simply dragging a file to the trash folder. It is securely deleting the files from every possible place which may serve as a technology platform for data restoration. There are a wide variety of methods which can help in secure data destruction. Some of them are as follows:
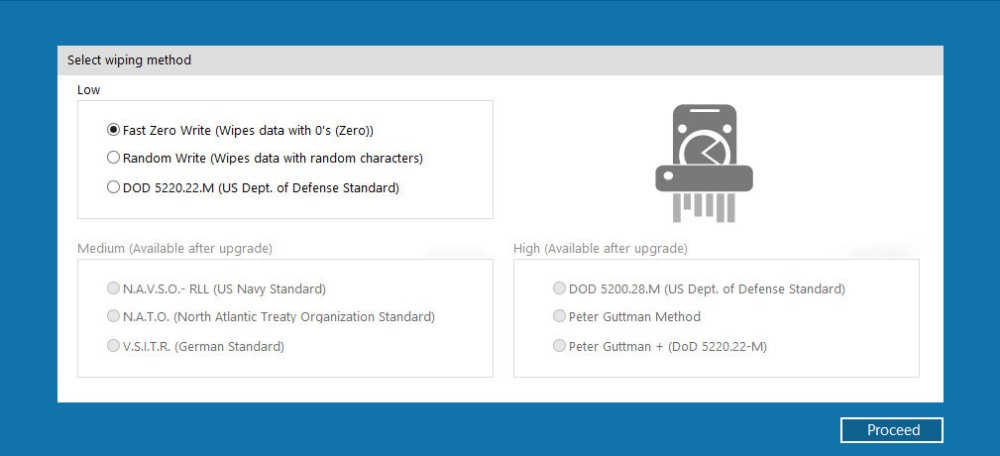
- Overwriting: Simply covering up your old data with information. Secure erasers are freely available at one’s service for overwriting hard drives.
- Degaussing: Erasing the magnetic field of storage media serves as another secure data destruction method. This involves the use of hard drives and back tapes. This service is usually offered by companies which run under the legislation of NISP, NIST and even particular Acts under which your organization is bound by law.
- Physically destructing the source of data storage: Techniques such as disk shredding are also a popular option. Industrial shredding machines can be used for grinding storage media files into tiny pieces of scrap metal which can then be sent for recycling.
The selection of data destruction method usually dependsup on the type of data or purpose. It is important to realize that every single bit of data ever stored in your PC or electronic device is present somewhere across history – in your hard drive or a memory chip, but it is still there! Guess what can the possibilities be of misusing this immensely personal data if not destructed properly?
- Imagine revealing your daily life routine to a complete stranger by carelessly disposing of your old mobile phone with a GPS tracker installed therein!
- Showing away your personal family photos and videos to hidden in your tablet or laptop.
- An old mobile phone or PC/laptop with Skype installed discarded with all those important meeting audio files stored.
Data destruction is the lye to moving forward technologically without being handicapped in future. Responsible companies today must be backed by strong and secured digital data destruction policies.
Pioneering Design for Education: Yanming Chen’s Innovative Approach to Vocabulary Apps






